Dear colleagues,
It is a pleasure announce that a new scientific paper has been published:
Abstract:
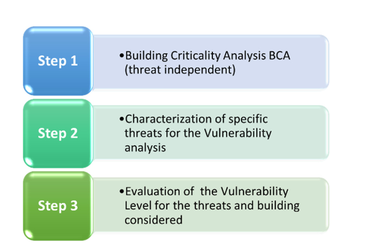
Assessing the vulnerabilities of a building/site for a specific threat is one of the key issues in the risk assessment process. A vulnerability is defined as any weakness that can be exploited by an aggressor to make an asset susceptible to damage. The purpose of the vulnerability assessment process discussed in this paper is to identify the main vulnerabilities which influence a buildings risk level when a specific explosive or chemical, biological, radiological (CBR) threat arises. Vulnerability assessments are designed to provide an in-depth analysis of the characteristics of a facility and its associated elements to identify building weaknesses and lack of redundancy, as well as to determine protective or corrective actions that can be designed or implemented to reduce building vulnerabilities. This work proposes an innovative building vulnerability assessment method (BVAM), comprised of three steps. The first step, building criticality analysis (BCA), seeks to verify the criticality of several building aspects elaborated from best practices on the analysis of building structure and function. The result of this BCA determines if critical building components or systems, designed for the deterrence, detection, and limitation of damages, can continue to function properly during a crisis, and to ensure the correct operation of the emergency systems. The second step aims at characterising the application of a given number of specific threats to the building. The third step focuses on a final assessment of the level of vulnerability associated with the various applied threats, for the specific building and the specific assets to be protected. This result is achieved by employing a proposed seven-level vulnerability scale. The result of the evaluation of the level of vulnerability can be used for the final risk assessment phase.
You can download here the paper and the whole book:

Write a comment